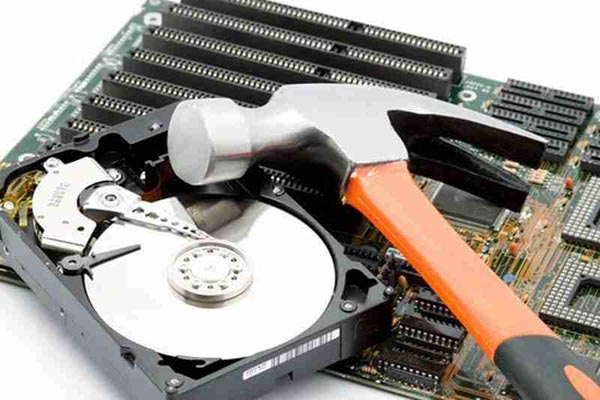
In today’s digital age, data security is of utmost importance. With the increasing threat of cyber attacks and data breaches, it is crucial to ensure that sensitive information is securely erased when it is no longer needed. This is where…
In the digital age, data is everything. From financial records to personal photos, we store our lives on our computers. But what happens when you need to get rid of that data? Simply deleting files doesn’t always mean they’re gone…
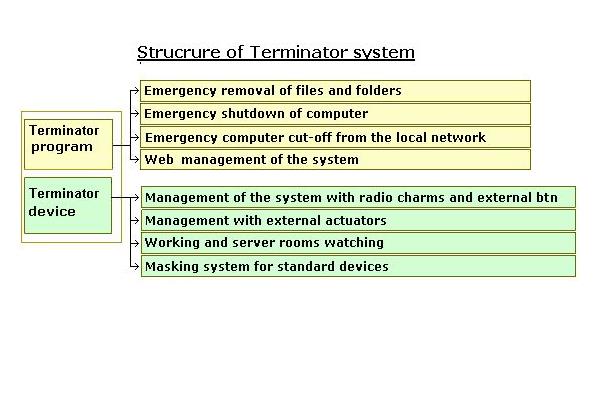
Terminator Program provides an opportunity to operate in a local network. In this case, the Terminator program itself can be run on any machine of the local network and become a server of Terminator network, while on client PCs the program Client,…
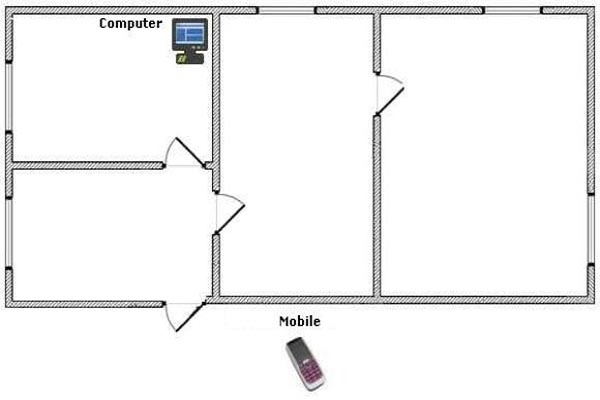
In today’s tough business world, where competition is sometimes regulated with dirty methods, special attention has to be paid to protect trade secrets. Those are accounting and legal documents, clients’ and other unique databases you need at your computer every…
Any specialist who understands the value of confidential information is wondering about rather undesirable effect of the private files falling into the wrong hands. And that is not the case that even legal business or Internet activities are under the omnipresent eye…
Three steps to implement control over Terminator Management via Internet are required. Configure the web server; Copy the checkrow to your mobile phone; Perform a remote connection to the server; Consider these steps in more detail. Settings panel of web…
The new SSD technology opens its doors to us. Operation speed, low power consumption and reliability of recording data aren’t all the benefits of this technology. There is at least another one. You haven’t seen such a reliable and fast…
In modern business dirty methods are common. Business competitors are extracting information in various ways. Data leakage is sometimes equivalent to a loss of business: if competitors receive that data, the damage would be non-recoverable. That’s why leaders of industry…
The turnkey solution for any office. Satisfactory reliability of protection. Turnkey solution: Removal of information can be performed: Automatically when you start Windows; By local network command; By pressing the hot key on the keyboard of PC; By mobile phone command; Options:…
The turnkey solution for large and mid-sized offices. Good reliability of protection. Turnkey solution: Removal of information can be performed: Automatically when you start Windows; By local network command; By pressing the hot key on the keyboard of PC; By mobile phone…