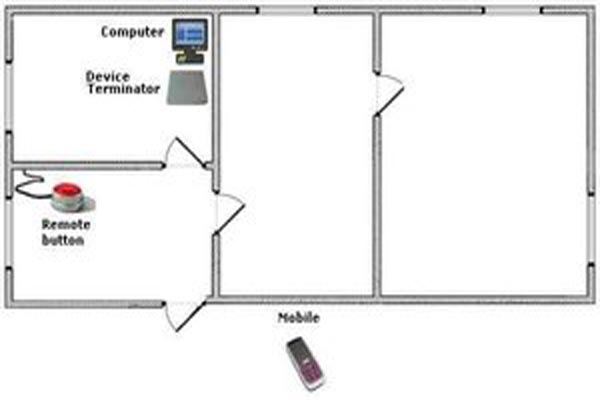
The turnkey solution for any office. Satisfactory reliability of protection. Turnkey solution: Removal of information can be performed: Automatically when you start Windows; By local network command; By pressing the hot key on the keyboard of PC; By mobile phone command; By…
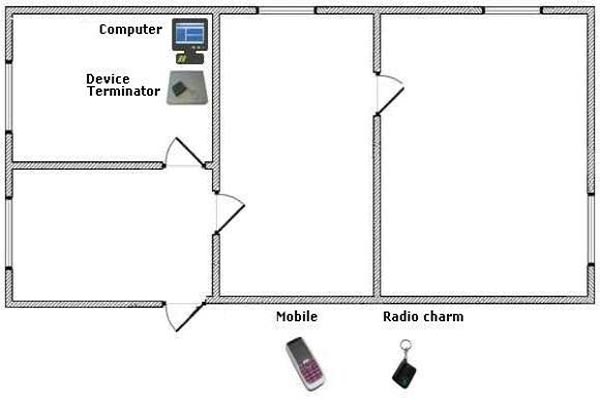
The turnkey solution for small and medium offices. Good reliability of protection.Turnkey solution: Removal of information can be performed: Automatically when you start Windows; By local network command; By pressing the hot key on the keyboard of PC; By mobile phone…
Current business environment demands new rules of game. Unfortunately, competitors may lend themselves to unfair practices, including espionage and even banal theft. That’s why these days the question of keeping trade secrets is so acute. Each organization has a bunch…
Nowadays, business people are very interested in saving confidential information. Everyone knows: if accounting, legal or business documents of the company would fall into unworthy hands, they can affect company’s welfare and its business image as well. That’s why permanent delete…
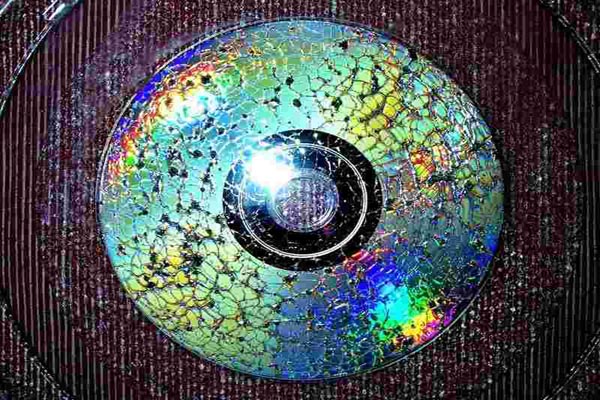
As we know, a file usually takes more than one cluster on a drive. When recording a file, clusters connect in a chain, wherein each cluster indicates the number of the next, comprising the following portion of this file. In…