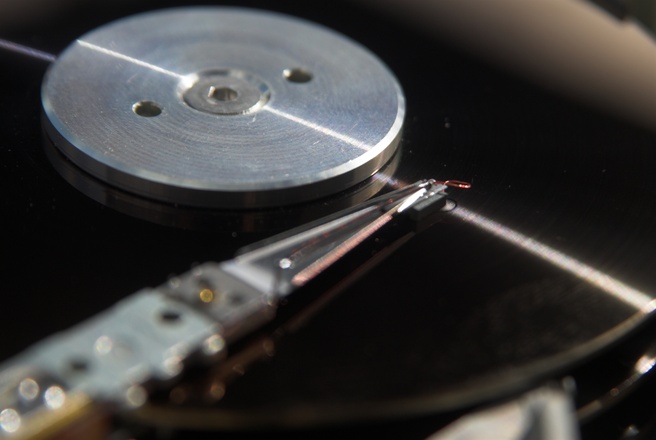
Terminator is a powerful program designed to erase file data on any hard drive within a network quickly, efficiently, and without the need for direct access to the computer. In times of emergency, when sensitive information needs to be removed promptly, Terminator comes to the rescue. With various activation methods such as web commands, local network commands, automatic triggers based on Windows events, user events, timers, and more, the process of removing information can be easily initiated.
The Versatility of Terminator
Terminator offers a range of features beyond its core function of removing information. It provides options to shutdown or restart the computer, automatically clean client computer drives from temporary files, close active processes, and even enable the computer to escape from the local network. This comprehensive set of functionalities makes Terminator a valuable asset for individuals and businesses alike.
One of the key advantages of Terminator is its ability to delete software without causing any damage to the hard drive. Unlike other programs that require frequent drive changes after each erase, Terminator ensures that your hard drive remains intact, saving you both time and money.
The Ease of Activation
Terminator simplifies the process of removing information by offering multiple activation methods. Whether you prefer to trigger the program through web commands, commands within the local network, or automatic triggers based on specific events, Terminator provides a seamless experience. It ensures that your data can be securely erased at a moment’s notice, regardless of the circumstances.
The program’s compatibility with Windows events and user events allows for effortless integration into existing workflows. By leveraging these triggers, you can automate the removal of sensitive information, enhancing your overall data security strategy. Additionally, Terminator’s timer functionality enables you to schedule information removal tasks, providing further convenience and peace of mind.
Enhance Your Data Security with Terminator
In today’s digital landscape, ensuring the protection of sensitive information is of paramount importance. With Terminator, you can take proactive steps towards enhancing your data security. By swiftly and thoroughly removing information from hard drives, Terminator mitigates the risk of unauthorized access or data breaches.
Furthermore, Terminator’s ability to shut down or restart computers, clean drives from temporary files, and close active processes adds an extra layer of security. These features prevent unauthorized users from accessing sensitive data that may be temporarily stored on the system.
Cost-Effective Solution
Terminator not only offers top-notch security features but also provides a cost-effective solution for data removal. Unlike other programs that require frequent hardware changes, Terminator ensures that your hard drive remains unaffected after each erase. This eliminates the need for unnecessary expenditures on new drives, saving you money in the long run.
Additionally, Terminator’s versatility and ease of use contribute to its cost-effectiveness. With its user-friendly interface and comprehensive functionality, Terminator streamlines the process of removing information, reducing the time and effort required to maintain data security.
Conclusion
Terminator is a powerful program that excels at removing information from hard drives within a network. With its versatile activation methods, comprehensive feature set, and cost-effective approach, Terminator offers a robust solution for individuals and businesses seeking to enhance their data security.
By leveraging Terminator’s capabilities, you can ensure that sensitive information is promptly and thoroughly erased, mitigating the risk of unauthorized access or data breaches. Furthermore, Terminator’s ability to shut down or restart computers, clean drives from temporary files, and close active processes adds an additional layer of security.
Invest in Terminator today and experience the peace of mind that comes with knowing your data is secure. Say goodbye to the worries of unauthorized access and breaches — Terminator has got you covered.<
CTA: Take control of your data security with Terminator. Visit our website today to learn more about our powerful program and how it can safeguard your sensitive information.